We know we’ve been pretty quiet in the last months — and even years 😇 — on the Engineering blog. But it’s a thing from the past as we’ve decided to come up with a bi-monthly post. Our goal is to provide a short diving into our latest technical changes and improvements every two months. Enough talk: here’s for the January and February 2022 roundup!
A new primary database
In the early days of January, we had the bad experience of getting some I/O errors on our primary PostgreSQL database. For reasons unknown to us, parts of the disks became unavailable for reading. They were immediate consequences: not only would some of our internal jobs fail, but we also became unable to perform new backups! This stressed the importance of having multiple types of backups. Thankfully, at any time we have:
- Daily pg_dump backups
- Daily complete backups using wal-g and PITR through the continuous archival of WAL files to a cloud storage
- A failover database.
Right after noticing the disks failure and prior to any user-facing problem, we created a new failover (our old one wasn’t large enough to handle the load comfortably) and started a wal-g restoration. We took this as an opportunity to:
- Review our restoration process with the engineering team
- Improve our failover database configuration
- Update our documentation around PostgreSQL backup and restoration
- Upgrade to larger instances.
Next time a similar event should occur, we’d be more prepared than ever.
Success in the 2022 Google Security Assessment
As our application requires two Gmail restricted scopes (gmail.readonly and gmail.compose) from users of Campaigns, we need to go through a yearly Security Assessment. Performed by the security company Bishop Fox, the assessment consists in testing our company, infrastructure, and application through 4 main prisms:
- Application Penetration Testing
- External Penetration Testing
- Deployment Review
- Policy and Procedure Review
This year, the researchers noticed that our security around the storage of OAuth tokens was insufficient in regards to the Google requirements. We promptly added an extra layer of security in enabling the GKE secrets at the application layer. This change introduces an extra layer of security to our Kubernetes configuration: Now, an attacker with access to etcd wouldn’t be able to read our secrets and would also need to gain access to keys managed by Cloud KMS.
This yearly assessment is an excellent confirmation that our infrastructure is secure and treats users’ data with care and respect.
Rails 7 upgrade
Hunter.io and api.hunter.io are both served by the same Rails monolith, created during Summer ‘15. From this date, we always made it a point of honor to upgrade Rails to its latest stable version available.
We didn’t change our habits with Rails 7, which was released on the 15th of December 2021. However, this upgrade required a bit more work than expected on two topics:
- Autoloading through Zeitwerk forced us to change a couple of
includedirectives - The change in default digest class for key generation in ActiveSupport, from SHA1 to SHA256, required us to rework our invocations of
ActiveSupport::MessageEncryptor.new(...)
This change being done, our plan for the next months is now to:
- Move to Ruby 3.1 (as we’re currently stuck with
protobufnot supporting Ruby > 3.1.dev) - Move away from Webpacker/Node/Yarn in favor of Import maps and Propshaft. Taking profit from the browsers enhancements and the assets pipeline we cherished makes us really excited!
- Move all the Javascript codebase to StimulusJS controllers. It’s still a long way to go, but we’re optimistic about reaching this point.
Focus on accessibility
At Hunter, we want our products to be usable by everyone. That’s why Web Accessibility matters to us. We know that we are not perfect on this subject but we recently decided to put more effort into it starting this year.
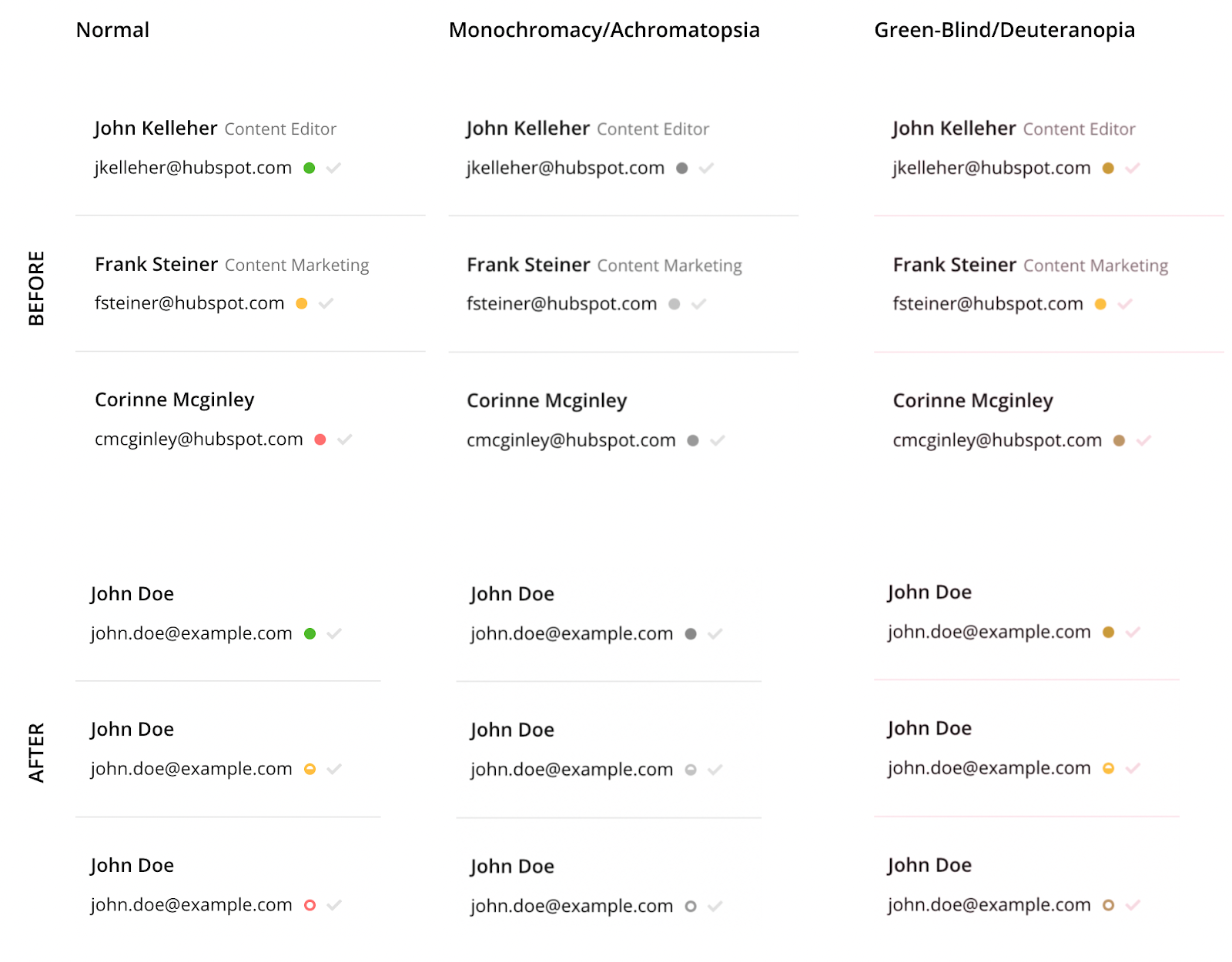
We already made some improvements. First, the confidence scores were reworked not to convey the information only by color, as required by the WCAG. Now, people with some vision problems or colorblindness will easily get the information just by the shape of the score.
Another improvement is that we reworked our colors to have broader palettes, better contrasts, and more consistency in our codebase. This change lets us introduce our first Design Tokens!
We took the advantage to eliminate the usage of SASS variables and move on to CSS Custom Properties (aka CSS Variables).
Customer stories
We love the way our customers use our products to improve their business. That’s why we decided to tell their stories to inspire other people.
We created a dedicated collection on our main blog, running on Ghost, to allow our marketing team to be autonomous in terms of content management. As customer stories are specific, they use a custom template.
You can discover our customer stories on hunter.io/customers.
That’s it for the January and February 2022 roundup! We really hope that you’ve enjoyed your reading, and we can’t wait to share with you more changes in improvements in the months to come.